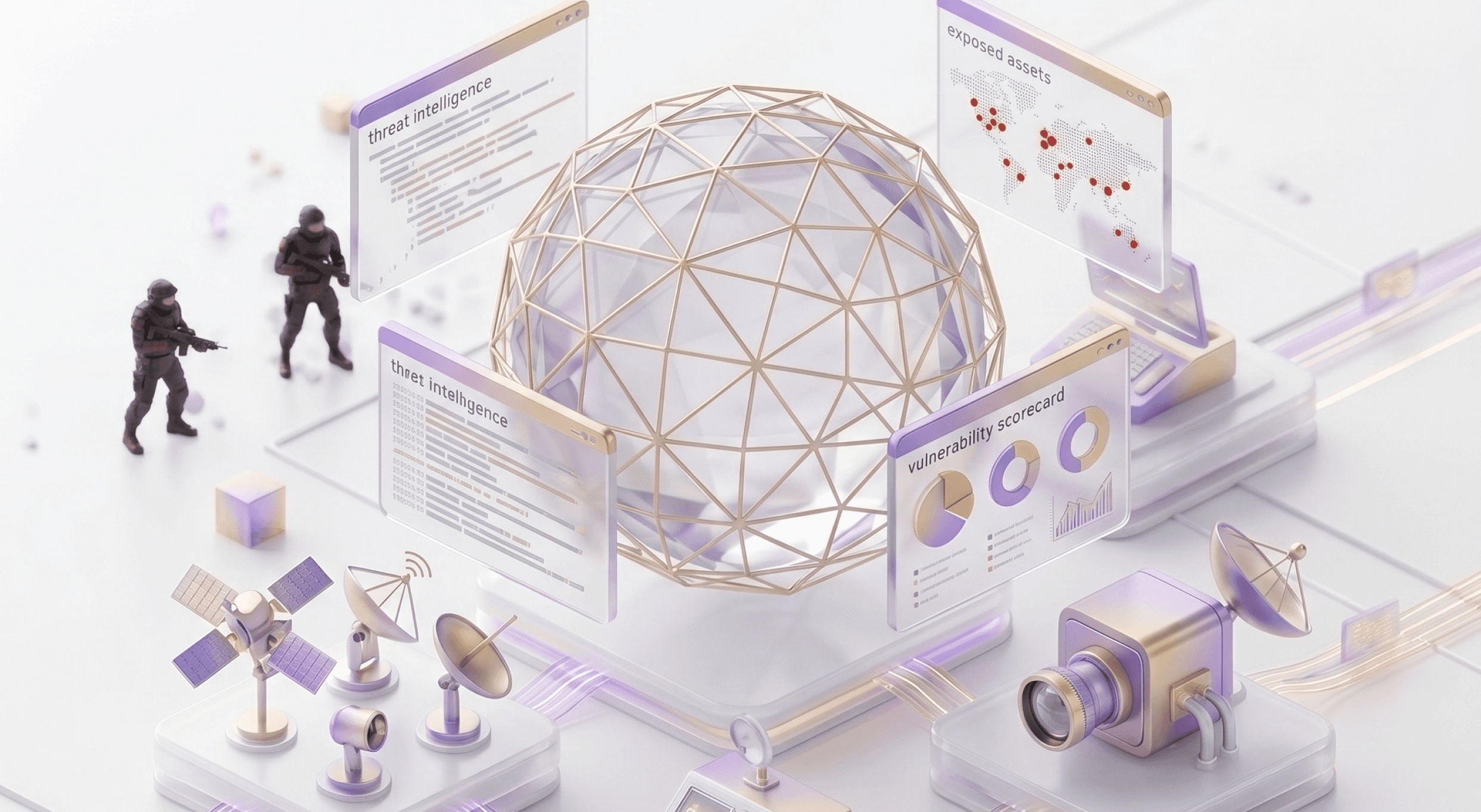
External Attack Surface Management.
Your eyes on the internet, helping you see what hackers see about you.
Our Offerings
How you stack up?.
Identify vulnerabilities across digital assets, secure against phishing and third-party risks, and ensure regulatory compliance—safeguarding your organization against evolving cyber threats. Sumeru assists you in monitoring your External Attack Surface by identifying and alerting you about digital risks through a tool called "Threat Meter". It detects issues such as:
Enquire
01
Identify external risks: DNS health, IP reputation, misconfigurations, and more.
02
03
04
05
06
Case studies
Real Results From
Real Engagements
Our Approach
It's easy to get started.
Improve your security program and make data-driven decisions to reduce cyber risk.
Submit Domain
Just submit your business domain to begin the scanning process.
Infrastructure Comb
We comb through your IT infrastructure to identify spots for improvement.
Free Report
Track exposed data across online file stores and criminal forums globally.
01
Start with a score
02
All-the-digital-assets
03
Get alerts
04
Fair deal
WHAT OUR CLIENTS SAY
Our clients love us and we keep giving them reasons to.
"
I am particularly impressed with their technical expertise in the Microsoft stack. They are driven to complete projects on time and give total attention to the accuracy of outputs.
Director
NettPositive
Security Manager
Shangri-La
"
Sumeru is our Information security partner! Their ability to align service delivery to business goals has directly helped us add value to our customers.
Paruchuri Raghukumar
TATA Power
"
Sumeru has assisted us in our ISO 27001 journey and has tailored a unique training module for our internal auditors. Their trainers are very committed and professional.
Sandeep Gangolli
LNTEBG
"
With your effective guidance, we were able to obtain ISO 27001 certification which resulted in improving our Information Security Standards.
TNGayathri, GM
Matrix Business Services
"
It was magnificent working with Sumeru.
Swathi Gaddala
Sutherland Healthcare Solutions







